“A month ago, I received a contact request on Skype from a woman in her early twenties. We quickly became intimate online. Then, she threatened to post some of my sexually explicit pictures on my employer’s social media profiles unless I transferred USD 600 to a third person in the Philippines. I did, fearing that she would jeopardise my employment. She demanded additional payments. I ended up informing my manager. Doing so was embarrassing.”
This experience, taken from a true-life online sextortion, can happen to anyone, not just to those who wittingly participate in the online activity described above. Advances in technology mean that online sextortionists can target a far broader audience. Online sextortion is increasingly affecting employees across all sectors, largely owing to the volume of targeting that perpetrators undertake. Given that online sextortionists continually evolve their tactics, how can individuals reduce their risk and limit the reputational and financial damage that online sextortion can cause?
Underreported crime
Despite authorities’ efforts to increase public awareness of this type of crime, online sextortion remains underreported. In 2018, the Anti-kidnap and Extortion Unit of the National Crime Agency (NCA) recorded more than 1,700 cases of sextortion in the UK alone. That same year, the NCA reported that at least five British men had killed themselves after falling victim to sextortion. The actual number of sextortion victims is thought to be significantly higher since most cases go unreported to law enforcement due to the potentially embarrassing consequences for the victim. According to the NCA, most perpetrators in these cases belonged to criminal groups based in the Philippines, Côte d’Ivoire and, to a lesser extent, Morocco.
In the US, the Federal Bureau of Investigation (FBI) recorded an increase in the number of reported online extortions in 2018. Most of the complaints handled by the FBI’s Internet Crime Complaint Center (IC3) in the same year were related to mass sextortion campaigns in the latter half of the year. These examples reflect only the tip of the iceberg when considered in the global context of sexually exploitive extortive activity.
Evolving tactics
Online perpetrators have almost always contacted targets via email, but they have only recently started to gain traction. In the early 2010s, online sextortionists would send batches of generic emails from a private domain to thousands of people. Most of these ended up in spam folders, or the targets ignored them. To increase success rates, perpetrators began to use familiar email domains such as Google, Microsoft and Yahoo to improve the chances of reaching their targets’ inboxes. They also began to alter the type of content – using images rather than text – and to employ translators for local languages to appear more convincing. The personal details they included, such as usernames and passwords in the subject and/or body of these emails, was (and can still be) found in historic data dumps (where stolen data is copied from the source and posted on open sources including paste sites) as well as sold on the dark web.
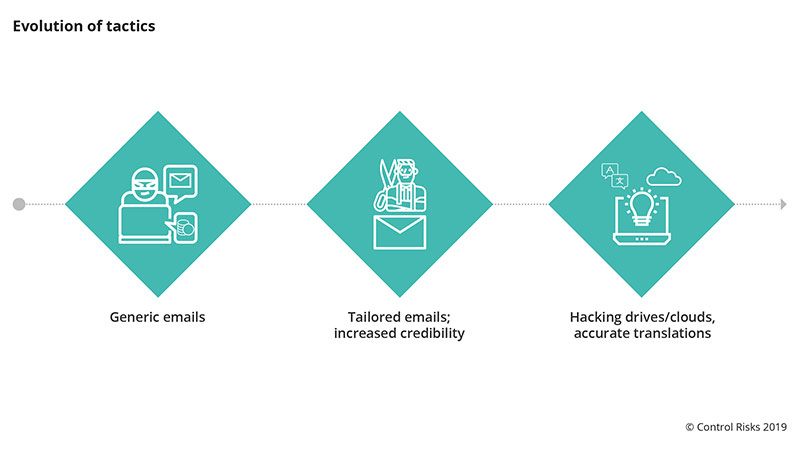
Now, online sextortionists more commonly send emails with sexually explicit photographs and videos that appear to – and in some cases do – contain valid images of the victim. They often obtain this content through hacking or romance scams.
In most hacking incidents, the victim has unwittingly installed spyware on his or her device. This allows the extortionist to access sensitive personal files and even to control the victim’s webcam. By controlling the device’s camera, the extortionists can then capture sexually explicit images of the target if they visit pornographic websites or engage in real-time video chats of a sexual nature. Online sextortionists have also proven their capability to send emails that purport to be from email and cloud storage providers and trick the targets into providing them with their usernames and passwords to these accounts, a technique known as phishing.
In romance scams, the extortionist develops an intimate relationship with their victim online, and eventually persuades him or her to perform sexual acts in front of a webcam, which the sextortionist records.
In most incidents of online sextortion, however, the extortionist does not possess any sexually explicit content of the target. Even if sextortionists have the intent and capability, it is often too time consuming for them to carry out spyware attacks or develop intimate relationships with their victims if they want to carry out high-volume attacks. Instead, they try to convince their victim of their credibility by revealing passwords to private accounts that they have obtained from data dumps as described above. This creates the illusion of having access to the target’s sensitive personal information.
In more sophisticated cases, the sextortionist claims to have sexually explicit content of the victim and sends him or her technically altered screenshots of videos from pornographic websites with the victim’s image superimposed into the scene. In cases where targets do not have a webcam, the images cannot be real. However, they may have posted innocuous photographs of themselves on social media platforms that extortionists have manipulated. We predict that, as sextortionists continue to capitalise on technological developments, cases of increasingly sophisticated image manipulation will rise.
Threats and demands
The success of this type of crime relies on the victim’s vulnerability. In the majority of cases upon which Control Risks advises, the extortionist threatens to send the sexually explicit content to the target’s partner, claiming to be their lover. In these cases, the extortionist reveals the partner’s name and contact details in their communications. However, Control Risks is also aware of incidents in which online extortionists have threatened to post the imagery on their employer’s pages on social media platforms or to email the sensitive content to the victim’s contact list. The sextortionists in these cases were sophisticated and had gathered information about the target’s professional connections beforehand, posing a reputational and financial threat to both the victim and their employer.
Online sextortionists have a short time to secure a ransom payment before the target works out it is a scam and/or contacts the authorities. As a result, they often demand a sum of money that victims can quickly pay. These demands frequently range between USD 200 and USD 1,000 and the payments are commonly requested via person-to-person transfer or in cryptocurrencies.
Managing the online sextortion threat
Online sextortion is here to stay; the risk/benefit ratio of this type of crime will remain favourable for the perpetrators. Tracing and identifying extortionists through the web is often difficult, and most sextortionists operate across international borders, which further minimises their risk of arrest. At the same time, the potential gains from this type of crime significantly surpass the perpetrators’ initial investment.
Online sextortionists will use increasingly sophisticated techniques to target employees across all sectors, posing a financial and reputational risk to them and their employers worldwide. Individuals can reduce the risk by familiarising themselves with sextortion tactics and monitoring advancements in how the crime is perpetrated. Organisations can support employees by encouraging them to report incidents to their management, despite the sensitivities, in order to get the right support. This may include access to specialist advisers in extortion and cyber security who – guided by a deep understanding of the wider cyber landscape – can help to determine the credibility of the threat, the extent of the extortionist’s operational capability, and the level of impact that the incident has had on the individual and the organisation’s business operations to inform an appropriate and effective crisis response.
